How to Read an Email Message Header
This blogpost volition explain how to read and sympathize the email header which travels with every email. It contains details about the sender, taken route and the receiver. Use this information to avoid unwanted emails or to recognize a scam or malware delivered by email.

How to access the Electronic mail Header
In the Mailfence web interface, get to your mailbox, right-click on the email, select 'View source'.
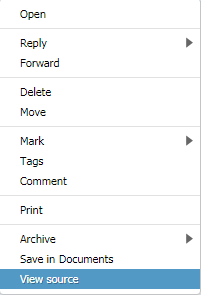
View message header – Mailfence
However, near mail clients allow admission to the message header. The following list contains a few popular email and webmail clients. In case not listed here, please refer to the manual of your customer.
View the Email Header in Google Mail (Gmail) Webmail:
Login to your business relationship via the web-interface and open the message (click on it). Click on the 'down-pointer' on the top-right of the message and select 'Show Original'.
View the Electronic mail Header in Yahoo Mail Webmail:
Login to your business relationship via the spider web interface and open the message (click on it). Click on 'Deportment' and select 'View Full Header'.
View the Email Header in Hotmail Webmail:
Login to your account via the web interface and go to the message list. Right-click on the message and select 'View Bulletin Source'.
View the Internet Headers in MS Outlook:
Open the message in MS Outlook. Now go to 'View' and select 'Message Options' – or 'File' -> 'Info' -> 'Backdrop'. Check 'Cyberspace Headers'.
View the Email Header in Thunderbird:
Open the message, and then click on 'View' and select 'Bulletin Source'.
View the Email Header in MS Windows Mail (and MS Outlook Express):
Select the message in the list, right-click on information technology and select 'Properties' and go to 'Details'.
Note: instructions mentioned above may vary depending on the version of the email client that you are using.
How to use E-mail Header Fields
We volition utilize the following sample message header. The font in blueish will describe what each of the common fields in an email header correspond, and how this data tin be used in a useful mode.
Standard Electronic mail Header Fields
Received: from sender_mail_server ([bbb.bbb.bbb.bbb]) past recipient_mail_exchanger (envelope-from <instance@gmail.com>) with ESMTPS
The message was received by the recipient_mail_exchanger from sender_mail_server with an IP address bbb.bbb.bbb.bbb over STARTTLS ('S' in the ESMTP tag means secure).
for <example@mailfence.com> ; Wednesday, 7 Sep 2018 12:35:32 +0200 (CEST) Return-Path: example@gmail.com
The mail server sends a notification e-mail to the address specified here, when the bulletin bounces or cannot be delivered. This email address is unlike from the sender's i and information technology results as "reply to" address.
Received: past xyz.google.com with SMTP id abc.xyz for <instance@mailfence.com>; Wed, 07 Sep 2018 03:35:32 -0700 (PDT)
Standard Email Header Fields (continued)
The message travels through all of these (ordinarily ane-3)mail servers (or MTA'southward) from sender_mail_server to the recipient_mail_exchanger.
Received: from 'Sender_display_name' ([aaa.aaa.aaa.aaa])
The message sent from the sender's device with the IP accost aaa.aaa.aaa.aaa. Located in theX-Originating-IP header field. In order to respect email clients, privacy removes the IP address, every bit it reveals sender's location details.
by sender_server_domain_name with ESMTPSA id abc_xyz_123 for <example@mailfence.com> (version=TLS1 zip=ECDHE-RSA-AES128-SHA bits=128/128); Wed, 07 Sep 2018 03:35:31 -0700 (PDT)
The sender_server_domain_name postal service server later on receiving a message from the sender's device with IP accost 'aaa.aaa.aaa.aaa', transfers the bulletin over STARTTLS (in the ESMTP tag, 'South' means secure and 'A' means authenticated). Information also includes the TLS version and cipher-suite that was used by the STARTTLS protocol.
Some might effort to fake the routing information, and your mail server is supposed to give you a alert that something was not right during the transfer from sender_server_domain_name to the recipient_mail_exchanger.
From: example@gmail.com
G essage sender address.
This could easily be faked, or could be made like examp1e@gmail.com OR case@gmai1.com ('1' and 'fifty' existence very similar).
Bank check our phishing and social engineering blogposts for more details.
To: case@mailfence.com
Message receiver accost.
Subject: Leaving Gmail!
Message subject.
Date: Wednesday, vii Sep 2018 12:35:29 +0200 Message-ID: 000601d30978hc36040$819a20c0$@gmail.com
Engagement and Message ID.
If the date mentioned here differs from the appointment mentioned in the concluding received header (top one), then it could signal possible message delivery issues OR an MITM attack. Therefore nosotros advice to pay circumspection in such cases.
MIME-Version: 1.0 Content-Blazon: multipart/culling;
MIME Version and Type.
X-Mailer: Microsoft Outlook 16.0
This message sent by the client electronic mail (or MUA) . In lodge to respect the email clients, privacy removes this line.
Content-Type: text/plain; charset="UTF-viii" Content-Transfer-Encoding: quoted-printable
This is a multi-role message in MIME (Multipurpose Net Mail Extensions) format. It is an Internet standard that extends the format of email letters to back up rich text, files and other active content.
<<Bulletin body>>
Hullo, Enough of privacy violations and shady business practices by Gmail! This is my concluding electronic mail from Gmail, as I finally decided to join Mailfence! Regards, Privacy conscious user! ------=_NextPart_000_0007_01D44514.EEC24AC0...------=_NextPart_000_0007_01D44514.EEC24AC0-- ...
<<Bulletin body>>
Bulletin body might comprise bad links like 'instance.com' which could be hyperlinked to 'maliciouslink.com'.
Check phishing and social engineering blogposts for more details.
Sender Policy Framework (SPF)
SPF is a framework to forestall sender address forgery. In add-on this platform describes mail servers that are allowed to ship messages for given (sender) domain. SPF thus helps to avoid fake sender electronic mail addresses. The event (Received-SPF) can be neutral, pass or fail.
From the sample bulletin above:
Received-SPF: laissez passer
Validation results is 'laissez passer' sincesender_server_domain_nameIP address sends emails for 'gmail.com' domain.
If the validation outcome is 'neglect', and then it is highly likely that someone tried to spoof the sender's email address and/or content.
Mailfence supports SPF and also encourages custom domain users to prepare one.
Domain Keys Identified Mail service (DKIM)
DKIM is a method to associate a domain name to an email. Furthermore it allows an system to check the (cryptographic) signature to ensure untampered transit of the bulletin. Thereby information technology ensures the ownership of the message.
From the sample message above:
DKIM-Signature: v=i; a=rsa-sha256; c=relaxed/relaxed; d=gmail.com; south=20161025; h=from:to:subject field:date:message-id:mime-version:thread-index :content-language; bh=fZjxO4TdlsVYWA6YIXoMF8AS+FOsm2lV1tfhDvYZNQo=; b=cMSUNWMGENp4jXuFTInBnZi6Sq2ZcjhBNA0ht8rSEt1SR8b0gGmiiZZ4l52lGSCum5 lRtmPPtt/tgnqubiLBBW2fatlarhjo6qRp7FRE9IsE6XBIl6muTGS/kUDwEm9NGXjQRp nxmHp4/JKDKrYHg8cKsm+yr3k17hNXHITIrb9VAh2CtEKpAxSYN3MsC4QplXdnLArQju U3jAnJf0lLZwZcygBbZSY7ENEAtHSbHpt6LLeQKlzosYARoakAH3j8EaAAAu1TfyAYE4 +u7ENqUzddifO6Qty3E2I4Soq00SbOO+e64WIUZ0gxoARQqeuAN7H/jaOkC4t5mhWmkb aEFA==
The message contains a valid DKIM signature (formatted as per the standard).
dkim=pass
Validation results is 'pass'.
If the validation result is 'fail', then information technology is highly likely that the message was spoofed or modified during transit and/or that the message is spam.
Mailfence supports DKIM for regular users by default. Also we encourage custom domain users to utilise it.
Spam score
Commonly used spam detection programs (e.thou., SpamAssassin) installed on the post servers provides a detailed report for each message. They do this by adding lines and a summary in the message header.
X-Spam-Flag: NO
Spam detection event.
10-Spam-Status: No hits=-1.two required=4.7
Spam detection result along with the score. A score less than v means (on nigh systems) not spam, between 5 and xv probably spam, and more than xv definitely spam.
symbols=BAYES_00,DKIM_SIGNED,DKIM_VALID,DKIM_VALID_AU,FREEMAIL_FROM,HTML_MESSAGE,RCVD_IN_DNSWL_NONE,RCVD_IN_MSPIKE_H2,RDNS_NONE,SPF_PASS device=ccc.ccc.ccc.ccc
Spam detection programs do not merely check the message sender, only as well check message format and the content of the message in order to derive their terminal spam score. East.k., bulletin structure, SPF+DKIM, DNSBL, custom rules…
If the overall spam score is between v and 15 or more than than 15, then it is highly probable that the message is suspicious or a spam. However, recipient_mail_exchanger makes the final decision.
On the email headers be many other approved message header fields as well as non-standard/custom message header fields. Some examples are:
- Authentication-Results –summary ofsender_server_domain_nameauthenticity (based on SPF, DKIM and other results).
- Listing-ID – an e-mail mailing listing reference
- Listing-Unsubscribe –a straight reference used to unsubscribe from a mailing list.
- Machine-Submitted – indication that a system generated the bulletin (east.g., notification letters, …)
- …
Email Header Fields and Terminate-to-end encrypted messages
Email message header fields are by and large read independently of the message body. Thus which is end-to-stop encrypted and is meant to exist read by the client (east.g., who holds the private key in a Public primal crypto-system). However, following are some of the common message header fields that can point an encrypted and/or signed bulletin.
From the sample bulletin above:
Content-Type: multipart/signed; micalg=pgp-sha1; protocol="awarding/pgp-signature" .... Content-Type: application/pgp-signature Content-Clarification: OpenPGP digital signature Content-Disposition: zipper
Indicates a MIME type 'multipart/signed' for OpenPGP signed bulletin which is sent as an attachment. OpenPGP signatures can also be sent inline (not as an zipper).
Content-Type: multipart/encrypted; protocol="awarding/pgp-encrypted"; ... Content-Type: application/octet-stream; name=encrypted.asc Content-Transfer-Encoding: ... (base64, 7bit, ...) Content-Description: OpenPGP encrypted message Content-Disposition: inline; filename=...
...
Indicates a MIME type 'multipart/encrypted ' for OpenPGP encrypted bulletin which is sent as an attachment. Send OpenPGP encrypted letters inline (not equally an zipper).
-----BEGIN PGP SIGNATURE----- ... -----END PGP SIGNATURE-----
Indicates the get-go and finish of an OpenPGP signature.
-----Begin PGP MESSAGE----- ... -----END PGP MESSAGE-----
Indicates the starting time and finish of an OpenPGP encrypted message.
Protecting email headers from end-to-end encryption
Utilise end-to-finish encryption and digital signatures to further check the legitimacy of message headers.
Mailfence includes the From, To and Fourth dimension-stamp fields in the message body before signing and/or encrypting it. This provides a way for the recipient to check:
![]() From: example@gmail.com
From: example@gmail.com
To: instance@mailfence.com
Sep 7, 2018 12:35:29
- If bulletin From and To addresses do lucifer with the sender and recipient addresses included in the signed and/or encrypted bulletin torso. Therefore, this helps in detecting whatsoever possible spoofing of sender/recipient address.
- If the message sending date matches (or is significantly close) with the time-stamp included in the signed and/or encrypted message body. This helps in detecting a possible message replay attack.
For example including the actual message header fields within an encrypted message torso tin can likewise help in preventing meta-data leaks (e.g., Protected email headers).
Many third party message header analyzer tools (https://testconnectivity.microsoft.com/, https://toolbox.googleapps.com/apps/messageheader/, https://mxtoolbox.com/EmailHeaders.aspx, …) produce an easy to read study from that bulletin header information. However, please note that you will take to share your bulletin header with these services…
Mailfence is a secure and individual email-suite that provides users full control over their data.
Follow u.s. on twitter/reddit and proceed yourself posted at all times.
– Mailfence team
Source: https://blog.mailfence.com/email-header/
0 Response to "How to Read an Email Message Header"
Post a Comment